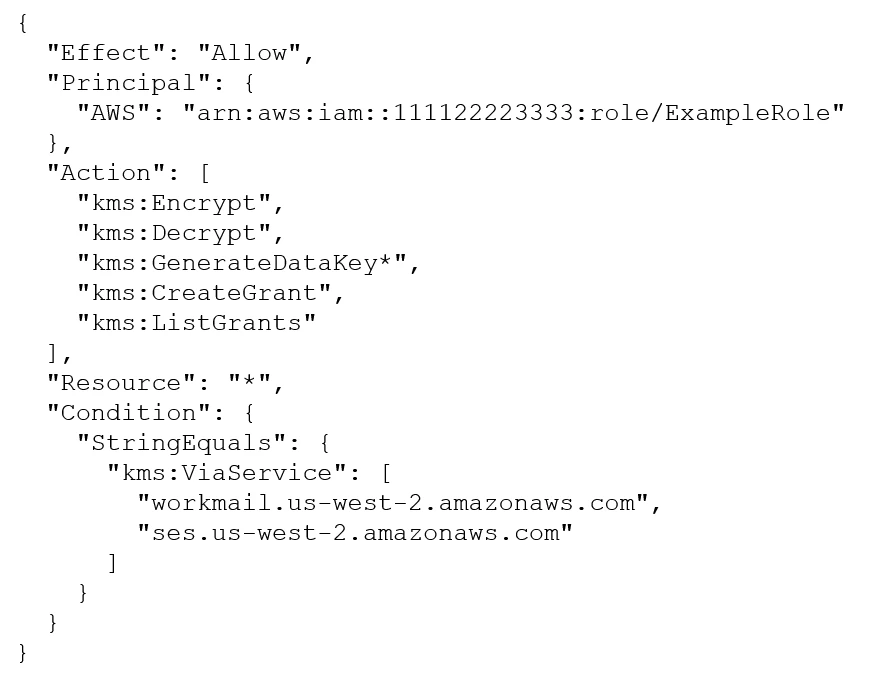
What is the effect of the following AWS Key Management Service (AWS KMS} key policy that is attached to a customer managed key?
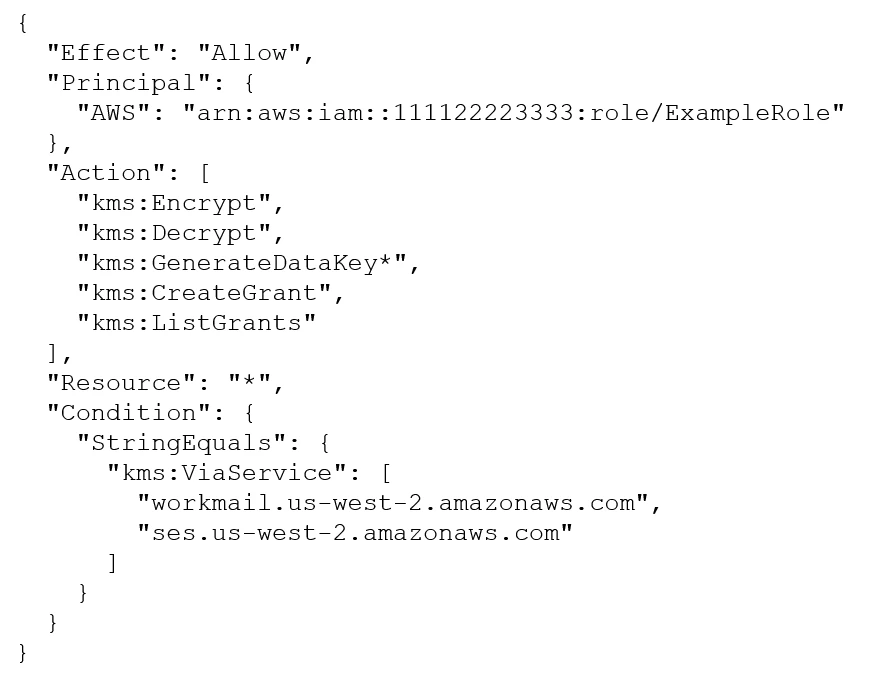
What is the effect of the following AWS Key Management Service (AWS KMS} key policy that is attached to a customer managed key?
A company wants to deny a specific federated user named Bob access to an Amazon S3 bucket named DOC-EXAMPLE-BUCKET. The company wants to meet this requirement by using a bucket policy. The company also needs to ensure that this bucket policy affects Bob's S3 permissions only. Any other permissions that Bob has must remain intact.
Which policy should the company use to meet these requirements?
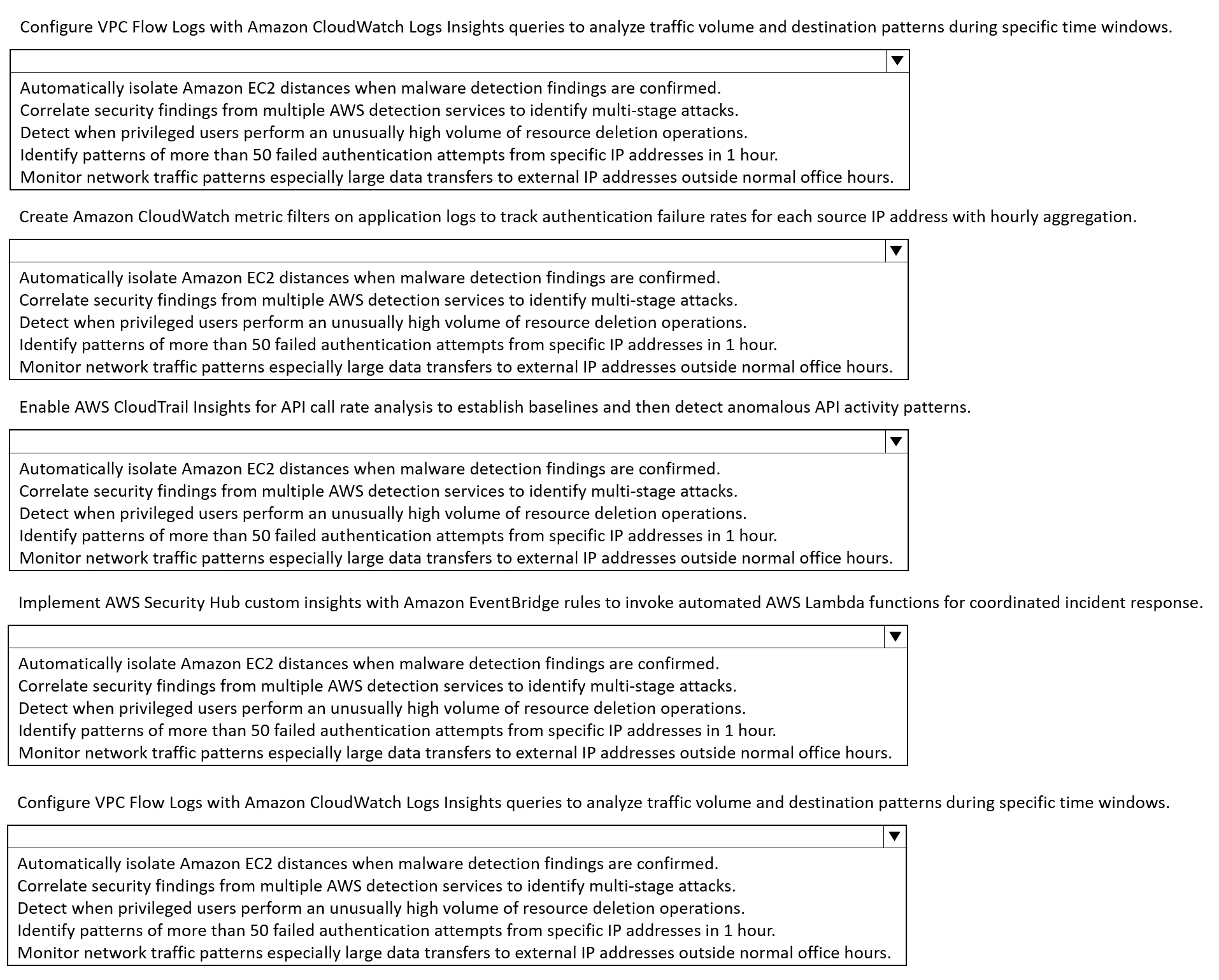
HOTSPOT -
A company is designing its security monitoring strategy for an existing sensitive workload on AWS. The security team has identified several scenarios that require monitoring strategies.
Select the correct monitoring strategy from the following list for each monitoring scenario. Select each monitoring strategy one time.
A company needs a solution to protect critical data from being permanently deleted. The data is stored in Amazon S3 buckets.
The company needs to replicate the S3 objects from the company's primary AWS Region to a secondary Region to meet disaster recovery requirements. The company must also ensure that users who have administrator access cannot permanently delete the data in the secondary Region.
Which solution will meet these requirements?
A security engineer is responding to an incident that is affecting an AWS account. The ID of the account is 1234156789012. The attack created workloads that are distributed across multiple AWS Regions.
The security engineer contains the attack. The security engineer removes all compute and storage resources from all affected Regions. However, the attacker also created an AWS KMS key. The key policy on the KMS key explicitly allows IAM principal kms:* permissions.
The key was scheduled to be deleted the previous day. However, the key is still enabled and usable. The key has an ARN of arn:aws;kms:us-east-2:123456789012:key/mrk-0bb0212cd9864fdea0dcamzo26efb5670. The security engineer must delete the key as quickly as possible.
Which solution will meet this requirement?