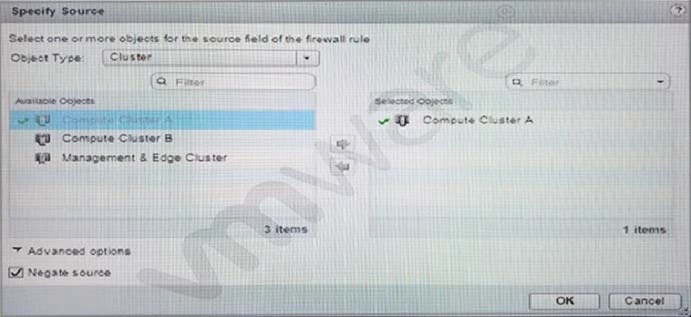
When specifying a source for a security rule, what is the purpose of the Negate Source check box?
What are two requirements of the network infrastructure to virtualize the access layer? (Choose two.)
Which vSphere network object abstracts the physical network, provides access-level switching in the hypervisor and enables support for overlay networking?
A network administrator has been tasked with deploying a 3-tier application across two data centers. Tier-1 and tier-2 will be located in Datacenter-A and tier-3 will be located in Datacenter-B.
Which NSX components are needed to make this deployment functional?