Which detection server is available from Symantec as a hardware appliance?
How should a DLP administrator exclude a custom endpoint application named “custom_app.exe” from being monitored by Application File Access Control?
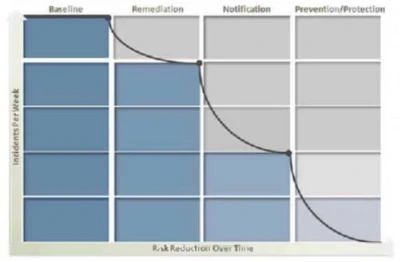
Refer to the exhibit. What activity should occur during the baseline phase, according to the risk reduction model?
How should a DLP administrator change a policy that it retains the original file when an endpoint incident has detected a “copy to USB device” operation?
Which two (2) of the following automated response rule types could be successfully executed by a policy who’s only detection rule is an Exact Data Matching (EDM) rule? (Choose two.)