The IT team has been tasked with updating the existing configuration to enforce captive portal authentication over a secure HTTPS connection.
Which two steps should the administrator take to implement this change? (Choose two.)
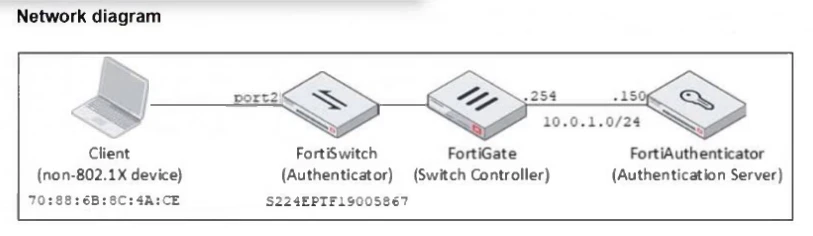
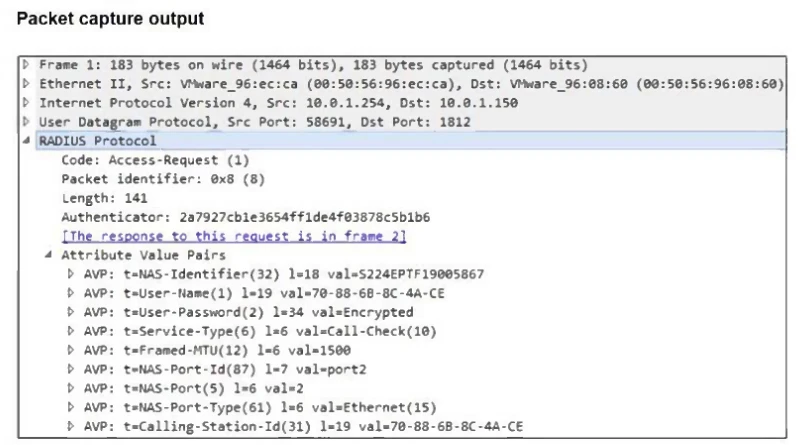
Examine the network diagram and packet capture shown in the exhibit.
During packet capture analysis, a RADIUS Access-Request packet was detected being sent from FortiSwitch to FortiAuthenticator and passing through FortiGate. The capture shows that the User-Name attribute in the RADIUS Access-Request packet contains the client MAC address.
Why is the client MAC address contained in the User-Name attribute of the RADIUS Access-Request packet?