What is a key advantage of cloning a virtual machine (VM)?
A company is using an intrusion detection and prevention system (IDPS) to scan and analyze intrusion events.
Which IDPS technique uses a database that contains known attack patterns?
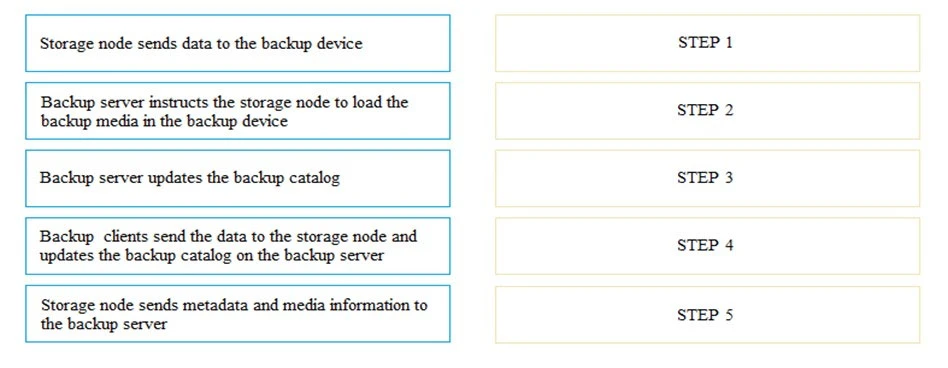
DRAG DROP -
In a backup operation, what are the correct sequence of steps after the backup server initiates the scheduled backup process?
Select and Place:
In an archiving environment, how is a content address created in a content addressable storage (CAS) system to store an object?
What is a benefit of link aggregation?