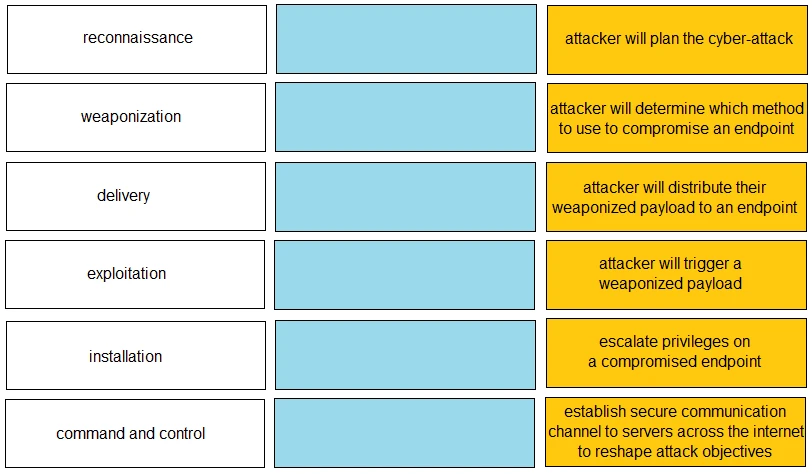
DRAG DROP -
Given the graphic, match each stage of the cyber-attack lifecycle to its description.

Select and Place:
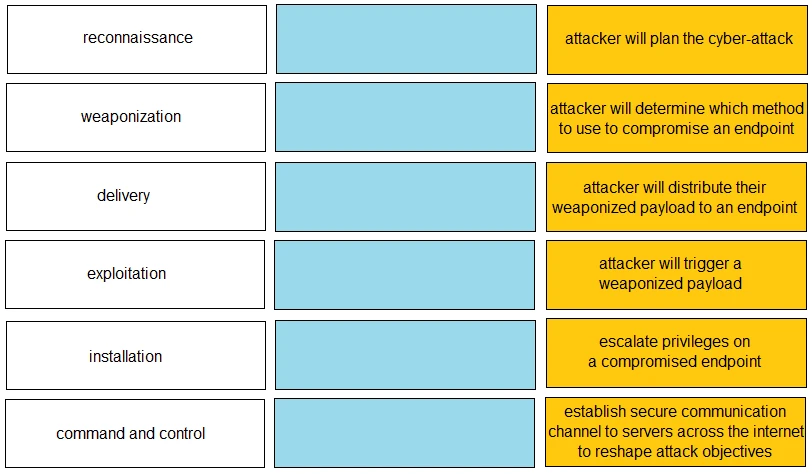
DRAG DROP -
Given the graphic, match each stage of the cyber-attack lifecycle to its description.

Select and Place:
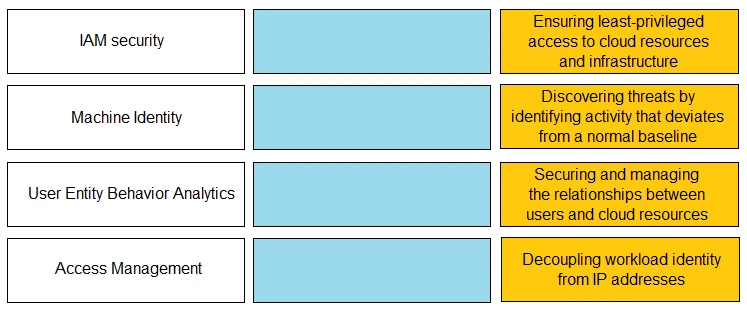
DRAG DROP -
Match the Identity and Access Management (IAM) security control with the appropriate definition.
Select and Place:
On an endpoint, which method should you use to secure applications against exploits?
Which not-for-profit organization maintains the common vulnerability exposure catalog that is available through their public website?
Which Palo Alto Networks tools enable a proactive, prevention-based approach to network automation that accelerates security analysis?