An administrator wants to exclude Request level logging details from being captured.
Which logging level must be set?
An administrator wants to exclude Request level logging details from being captured.
Which logging level must be set?
An administrator wants to ensure that a datasource can be referenced when creating data modules in the IBM Cognos Analytics Portal (New > Data module).
What must be done to accomplish this?
An administrator wants to render a report and ensure the completed HTML is sent back to the gateway.
Which service is responsible for the rendering task?
An environment has the following routing rules set:
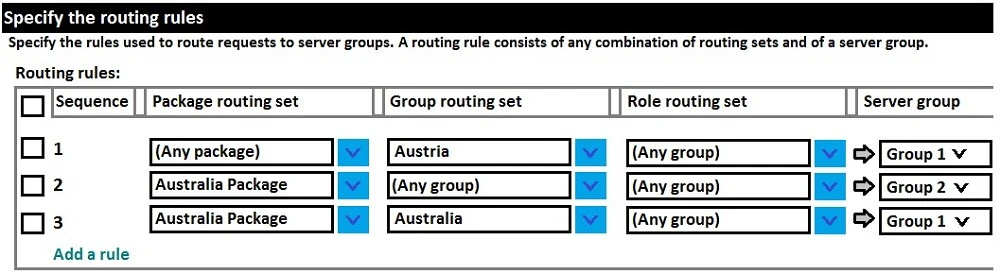
If a report using the Australia Package is run by a user belonging to Australia Group, which server group will the request be sent to?
All users have unrestricted access in a secured environment.
What must be modified to control this access?