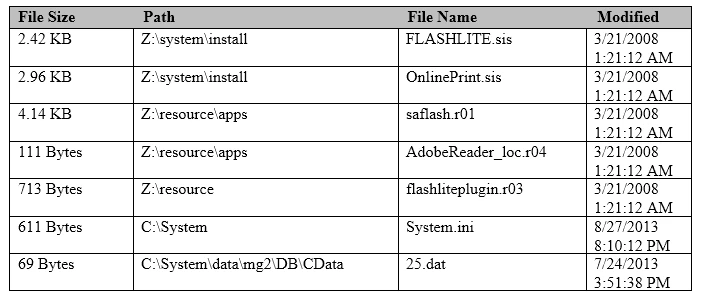
An analyst investigating a Nokia S60 Symbian device wants to know if an Adobe Flash file on the handset is compromised. Which file in the image will best target the Adobe Flash files?
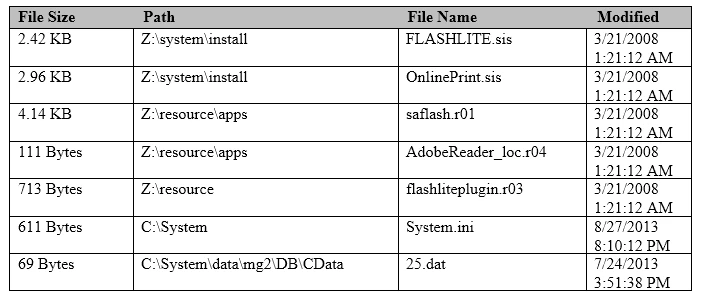
An analyst investigating a Nokia S60 Symbian device wants to know if an Adobe Flash file on the handset is compromised. Which file in the image will best target the Adobe Flash files?
As part of your analysis of a legacy BlackBerry device, you examine the installed applications list and it appears that no third-party applications were installed on the device. Which other file may provide you with additional information on applications that were accessed with the handset?
Which artifact must be carved out manually when examining a file system acquisition of an Android device?
When conducting forensic analysis of an associated media card, one would most often expect to find this particular file system format?
Cellebrite Physical Analyzer uses Bit Defender to scan for malware by flagging files who have known bad hash values. This is an example of which type of mobile malware detection?