What is a possible reason?
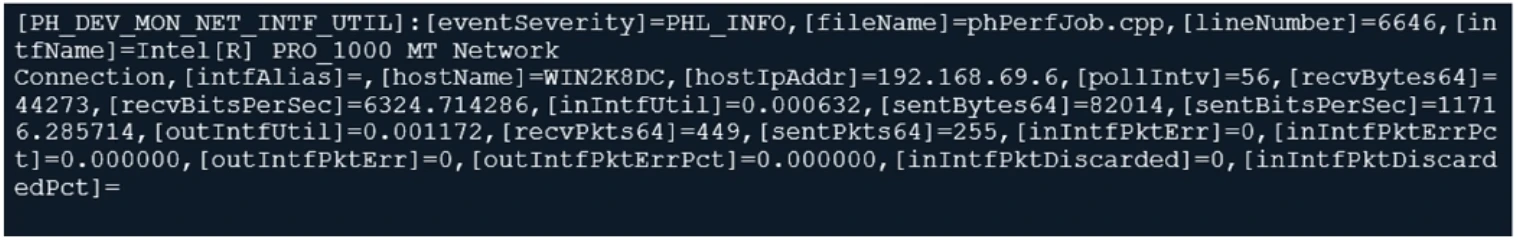
From your analysis of the output, which statement about the output is true?
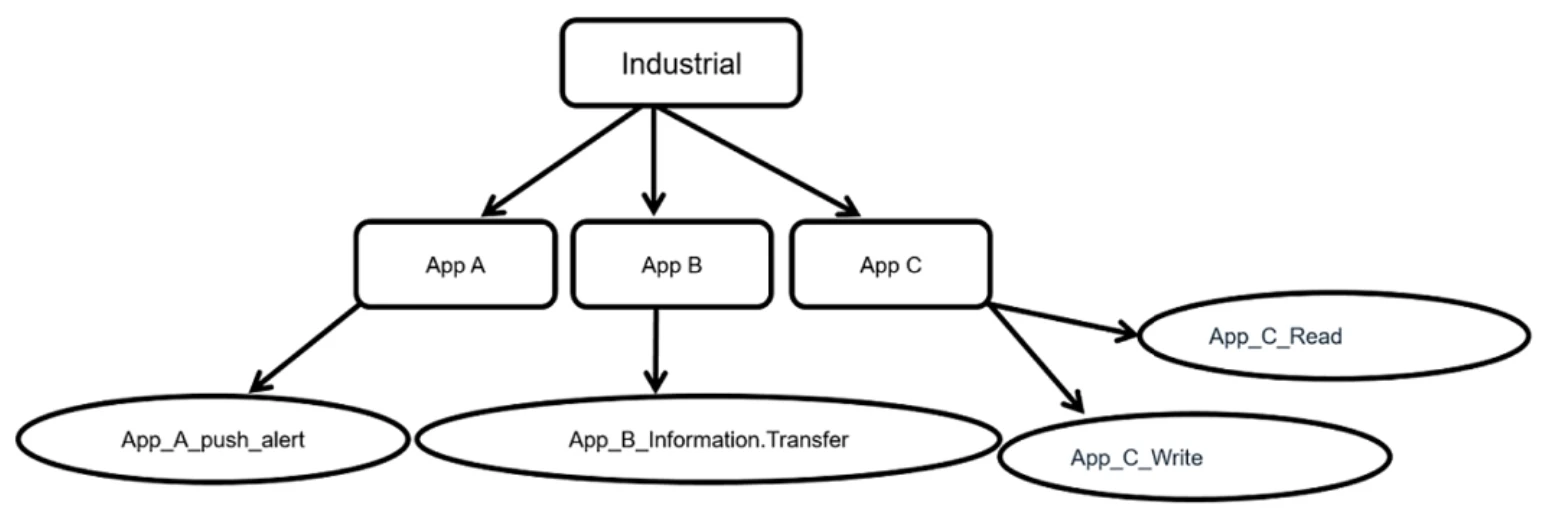
Which statement is true about application control inspection?
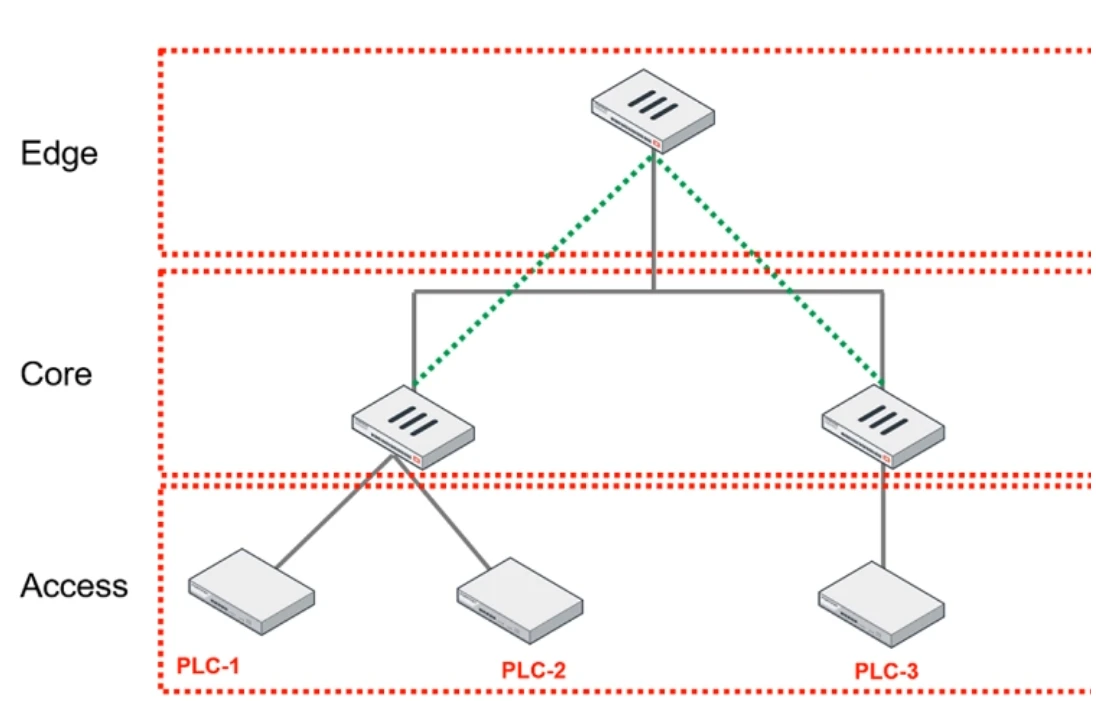
You are assigned to implement a remote authentication server in the OT network.
Which part of the hierarchy should the authentication server be part of?
Which statement ensures security protection is in place for all ICS networks?