The security officer is given a list of all assets. According to NIST, which two elements are missing to calculate the risk assessment? (Choose two.)

Refer to the exhibit. At which stage of the threat kill chain is an attacker, based on these URIs of inbound web requests from known malicious Internet scanners?
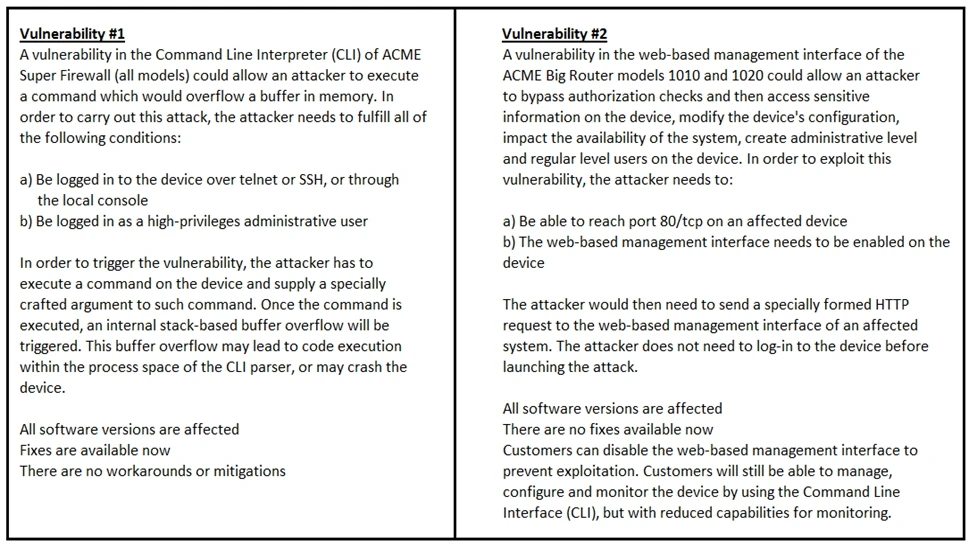
Refer to the exhibit. How must these advisories be prioritized for handling?
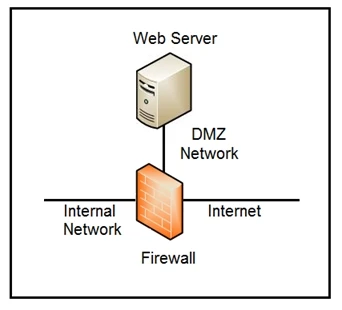
Refer to the exhibit. Which two steps mitigate attacks on the webserver from the Internet? (Choose two.)