The engineer decides to implement dynamic secrets.
Which method helps to get this implementation accurate from a security point of view?
Which data work flow is appropriate for how the critical and non-critical data is processed?
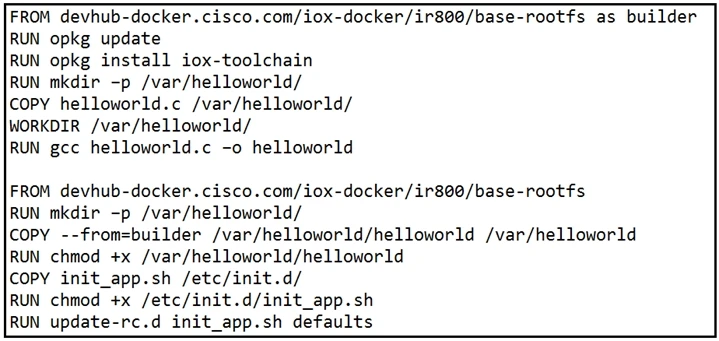
Refer to the exhibit. When a Docker image is built using this Dockerfile, which two statements are valid on Cisco IOx 1.8 and before? (Choose two.)