SIMULATION -
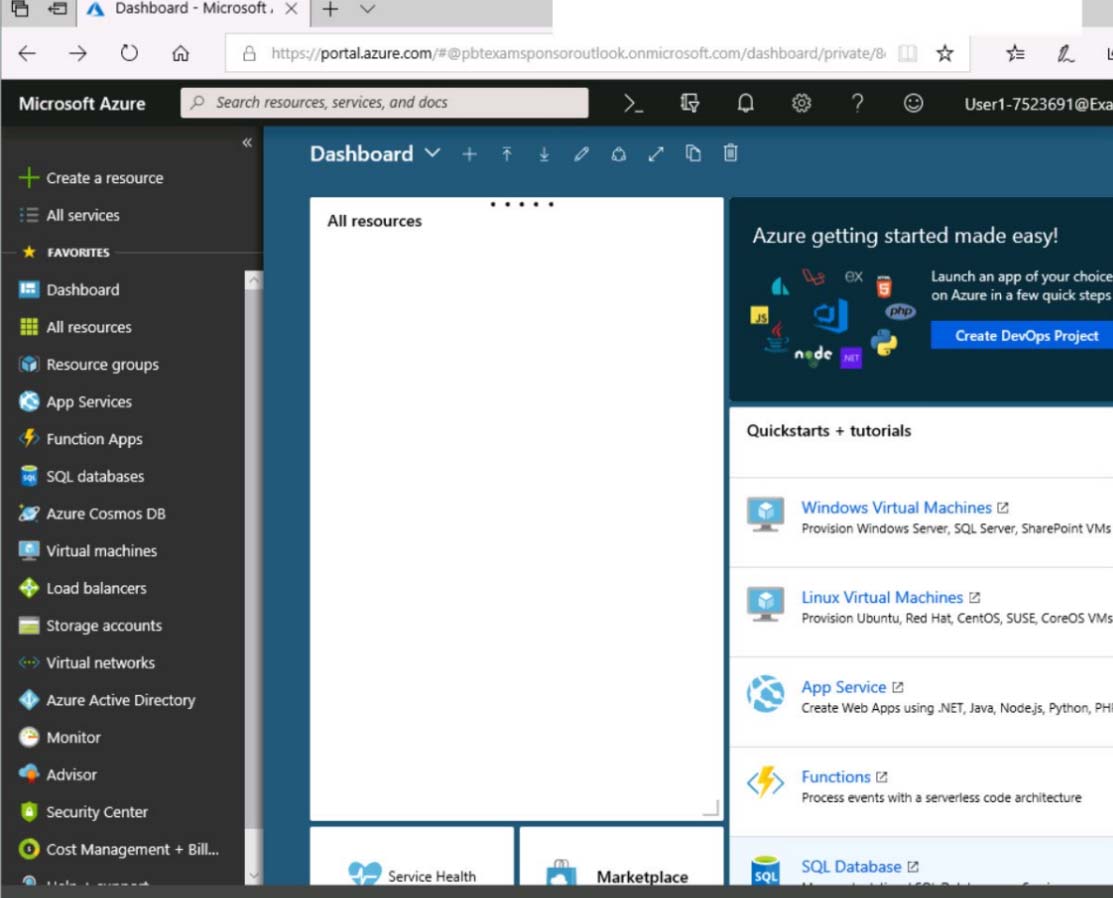
Click to expand each objective. To connect to the Azure portal, type https://portal.azure.com in the browser address bar.

When you are finished performing all the tasks, click the "˜Next' button.
Note that you cannot return to the lab once you click the "˜Next' button. Scoring occur in the background while you complete the rest of the exam.
Overview -
The following section of the exam is a lab. In this section, you will perform a set of tasks in a live environment. While most functionality will be available to you as it would be in a live environment, some functionality (e.g., copy and paste, ability to navigate to external websites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn't matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may have more than one lab that you must complete. You can use as much time as you would like to complete each lab. But, you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please note that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
To start the lab -
You may start the lab by clicking the Next button.
You plan to host several secured websites on Web01.
You need to allow HTTPS over TCP port 443 to Web01 and to prevent HTTP over TCP port 80 to Web01.
What should you do from the Azure portal?