Scenario: A Citrix Architect must complete a XenApp and XenDesktop security assessment. After examining the network topology for the hypervisor hosts supporting the Virtual Delivery Agent (VDA) machines, the architect finds that some of the network connections are NOT following leading security practices.
Click the Exhibit button to view a high-level diagram which shows the connectivity between various components.
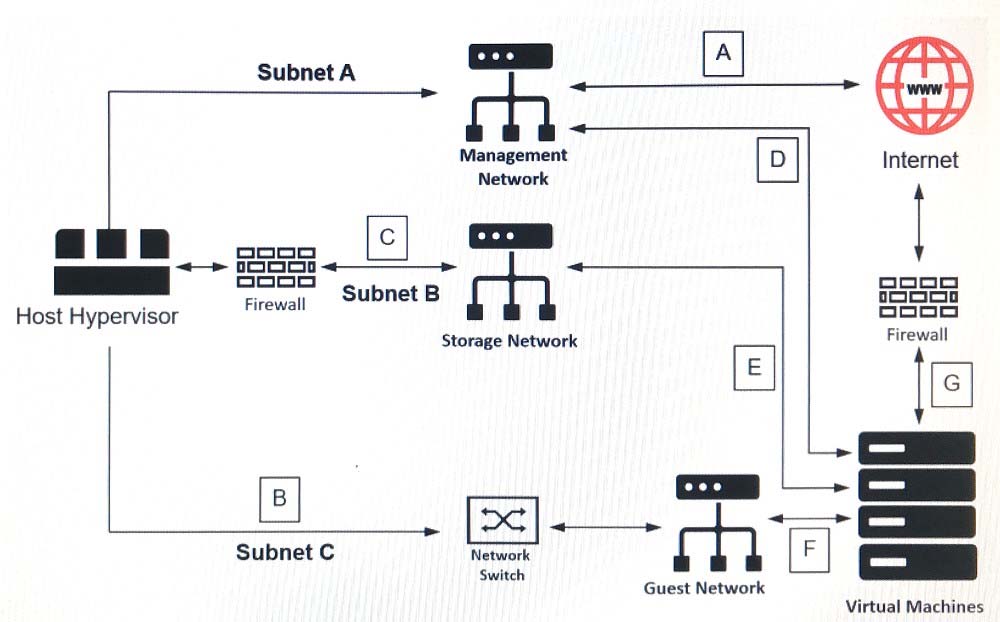
Which three of the labeled areas of the diagram represent connections which are NOT following Citrix leading security practices? (Choose three.)