Which of the following must the company do to ensure GDPR compliance? (Choose two.)
Which of the following is the MOST likely cause?
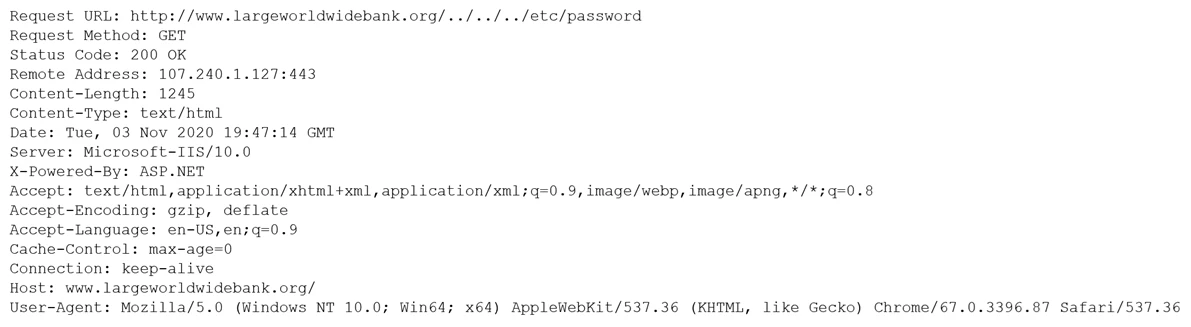
Which of the following would BEST mitigate this type of attack?
✑ Supporting MFA against on-premises infrastructure
✑ Improving the user experience by integrating with SaaS applications
✑ Applying risk-based policies based on location
✑ Performing just-in-time provisioning
Which of the following authentication protocols should the organization implement to support these requirements?